Boot failure: /init: line 256: /sbin/zpool: Text file busy (AMD 7950x3d)
Over the last couple of months I'd noticed a strange message which appeared at boot time:
error: out of memory.
Press any key to continue...Up until now I hadn't had to do anything except let the system sit for a few seconds as it would appear to 'self-correct' and boot me into Ubuntu 22.04. Today I experienced a different issue where my zfs root partition will not mount and I'm dropped to a busybox shell and left to wonder what went wrong?
Begin: Running /scripts/local-premount ... done.
[ 8.710953] ZFS: Loaded module v2.1.5-1ubuntu6, ZFS pool version 5000, ZFS filesystem version 5
Begin: Importing ZFS root pool 'rpool' ... Begin: Importing pool 'rpool' using defaults ... Failure: 126
Begin: Importing pool 'rpool' using cachefile. ... Failure: 126
Command /sbin/zpool import -c /etc/zfs/zpool.cache -N 'rpool'
Message: /init: line 256: /sbin/zpool: Text file busy
Error: 126
Failed to import pool 'rpool'.
Manually import the pool and exit.When I try to directly re-run the zpool command above, I get a Text File Busy error, which is entirely unhelpful...
(initramfs) /sbin/zpool import -c /etc/zfs/zpool.cache -N 'rpool'
Message: /init: line 256: /sbin/zpool: Text file busy
Error: 126Eventually I was able to find the solution to my boot issue.
How to Configure the Mikrotik hAP ax lite as a WiFi Client (WPA2-Enterprise)
I'll be at DEF CON 31 next week and in preparation for the event have upgraded my portable wifi router to a Mikrotik hAP ax lite. My preference is to have a separate device handle WiFi connectivity to conference networks and use wired connectivity to the various devices I like to operate during the event. What I like about the hAP ax lite is that it is powered through a USB-C connector and includes the capability to act as a WiFi client to pass traffic back to the 4 ethernet jacks provided on the back of the unit.
As this is my first time configuring a Mikrotik router, I want to document it for future reference.
Linux: Flashing Firmware on the DC Darknet Badge for DEF CON 31
Being the contrarian that I am, I don't run Windows or Mac OS on any of my workstations. As a result my path to flashing firmware on the DC 31 Darknet badge is a little more complicated. This post walks through what I did to get the badge setup without using the 'web flasher'.
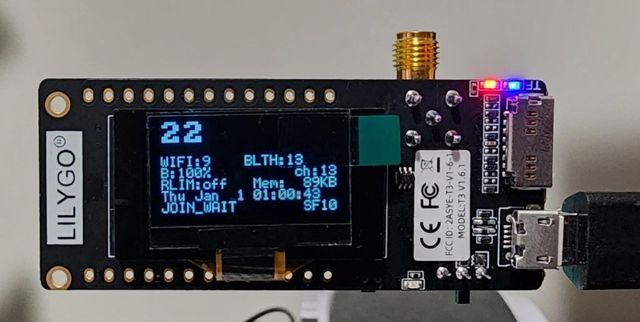
Here's a picture of the device:
First steps towards MLOps: Goals, Setup and Initial Operation of an OSS model locally
Back in February I started to take an interest in Artificial Intelligence (AI) given the then recent developments in the field. Since then there has been an explosion of generalized interest in Large Language Models (LLMs), which from where I sit started with the leak of Meta AI's Llama Model. At the time I made a mental note to return later in the year (when I had time) to play around with the technology and investigate applications of Generative AI... Months passed on by with high priority / high stress work commitments dominating my waking hours, culminating in a week long offsite in June.
I resolved to take a 'bi-modal' approach to learning and applying machine learning / AI technology:
- Gain an understanding of the art from first principles to form a foundation for effective use of the technology
- Download, deploy and apply available technology to gain experience in the application of Generative AI
It might come as no surprise to note that this approach lends itself towards unique challenges as I interleave time to both of these avenues of investigation.
This post describes what steps I took to build out a 'functional' ML stack sufficient to download and run freely available LLMs.
Create a keyfile encrypted ZFS volume in Ubuntu 22.04
For the first time in nearly a decade I assembled a new desktop workstation to support a growing interest in learning about Artificial Intelligence and Machine Learning from "first principles". This is a departure for me, having been a creature of laptops for many years. To make things more interesting a ZFS pool will be used in place of the usual 'RAID' array for my large storage disks.
This post walks through how to create an encrypted ZFS pool / dataset (still adjusting to the terminology) which is auto-mounted on system boot
Kindle Oasis does not connect to home WPA2-Enterprise Network
My Kindle Oasis (3rd generation) decided to stop connecting to my home WiFi network today. It displayed a cryptic message about not being able to connect so I investigated. Logging in to my Ubiquiti console I did not notice any attempted logins. Checking pfSense / FreeRADIUS also turned up zero log events. The Kindle itself did not provide any log messages...
The best I had to go on was a hunch: A few months back I had issues with my Android devices after a security patch blocked connections to WPA2 Enterprise networks without specifying a CA Certificate. Could that be the problem here?
Update (2023-04-08): After configuring the CA Certificate the Kindle connected, self-updated then failed to connect again. Additional detail added below
Thoughts on System Design and the 'Organic' Emergence of Security Requirements
I've been thinking about the classic 'InfoSec Triad' lately (Availability, Integrity, Confidentiality) and how challenging it is to convey the real-world value of these concepts during real-world discussions on how to 'secure' a system. The InfoSec industry could stand to improve by providing clear provenance for each 'Security Requirement' that gets proposed. Most security professionals struggle to convey information security theory to non-specialists.
In this post I explore a 'hypothetical system' and attempt to show where security concerns become surfaced during the lifecycle of a growing software system. Not all systems will have the opportunity to grow to a point where designers need to seriously consider the more complicated an 'fun' security angles.
Upgrade to NextCloud 23 prevents online document editing in Collabora online: Files download instead of edit
After my recent effort in upgrading gitlab I decided to take a crack at updating NextCloud to version 23. On the surface it all went well - upgrading the dockerized version from 21 → 23 went smoothly and without any obvious errors.
Unfortunately, it appears that online document editing a-la Collabora Online [w/ Built-in CODE Server] has a problem when performing an upgrade installation. When attempting to edit a document in-browser I am prompted to download the file - no in-browser editor appears to load(?).
Ever Stale: A Tale of missed updates or how to upgrade GitLab from 12 to 14
I spent an hour reviewing my home lab setup and found an old internal gitlab instance running that I hadn't touched in some time. It was running GitLab-CE 12.10.13-ce.0 and was ready for an update! The latest version of GitLab at the time of this writing is 14.5.2-ce.0 which was too far to take in one jump. A complicating factor is that I've run this server since version 8.x using their publicly available docker image and have not built it out in a way that lends for easy upgrades. Fortunately I was able to apply the updates, not without some drama.
Today's ‘modern’ approach to application deployment can leave you in a perpetually stale state if you aren't able or willing to keep up with the relentless onslaught of patches, updates and troubleshooting patch/update failures.
BSidesSLC 2021: Container Security From the Bottom Up
Most companies have experimented with containerization in one form or another and there is a wealth of information at these higher abstraction levels for securing constructs like Dockerfiles, Container Images, and Container Orchestration tools like Kubernetes. What can be overlooked at times is that...
